Uncompromising security for high-stakes diligence.
We built CodeDD to secure the transaction. Our ephemeral architecture ensures that intellectual property is analyzed deeply but never retained.
For Target Companies
Zero-Retention Guarantee
Your Intellectual Property is your most valuable asset. We do not store your source code. CodeDD utilizes a volatile memory architecture where repositories are streamed, analyzed in isolation, and immediately wiped from existence upon report generation.
- No permanent storage of source code.
- Ephemeral, sandboxed analysis environments.
- Exclusion of proprietary business logic from model training.
For Investors & Advisors
Institutional Data Governance
Conduct diligence without the liability of data custody. Our platform provides the audit trail and scalability required by Investment Committees, secured by enterprise-grade encryption and strict access controls.
- ISO 27001 & SOC 2 aligned controls.
- End-to-end encryption (TLS 1.3 & AES-256).
- Role-Based Access Control (RBAC) for Deal Teams.
- Data Residency in Europe (IONOS)
Enterprise-Grade Protection
Our infrastructure is designed to withstand the rigorous demands of institutional finance and enterprise technology.
Infrastructure Isolation
CodeDD runs on single-tenant containerized instances. Each audit occurs in a fresh, isolated environment that shares no state with other clients or analyses.
Encryption Standards
Data is encrypted in transit via TLS 1.3 and at rest using AES-256. API keys and repository credentials are managed via strictly governed vault services.
AI Model Privacy
Our analysis models are frozen. We do not use client code submitted for diligence to train, fine-tune, or improve our base foundation models.
Access Governance
Strict identity management integration allows Deal Teams to manage granular permissions. Support personnel have zero standing access to client data.
Vulnerability Management
We subject our own platform to the same rigour we apply to yours. Continuous automated scanning and third-party penetration testing ensure platform resilience.
Data Residency
For sensitive cross-border M&A, CodeDD offers region-locked processing to ensure compliance with GDPR, CCPA, and local data sovereignty requirements.
Compliant with Industry Standards and Regulations
Independent penetration testing
External security validation of the CodeDD platform.
Secure Audit Process
CodeDD is designed from the ground up to protect your most valuable IP - your Source Code. See below the entire process to understand the audit process in its entirety.
Audit Request
Audit Request
You received a request to audit your codebase. To start the audit, you will need to provide your git repository URL.
Multiple repositories can be audited at once, and you can add as many as you want to the audit queue.

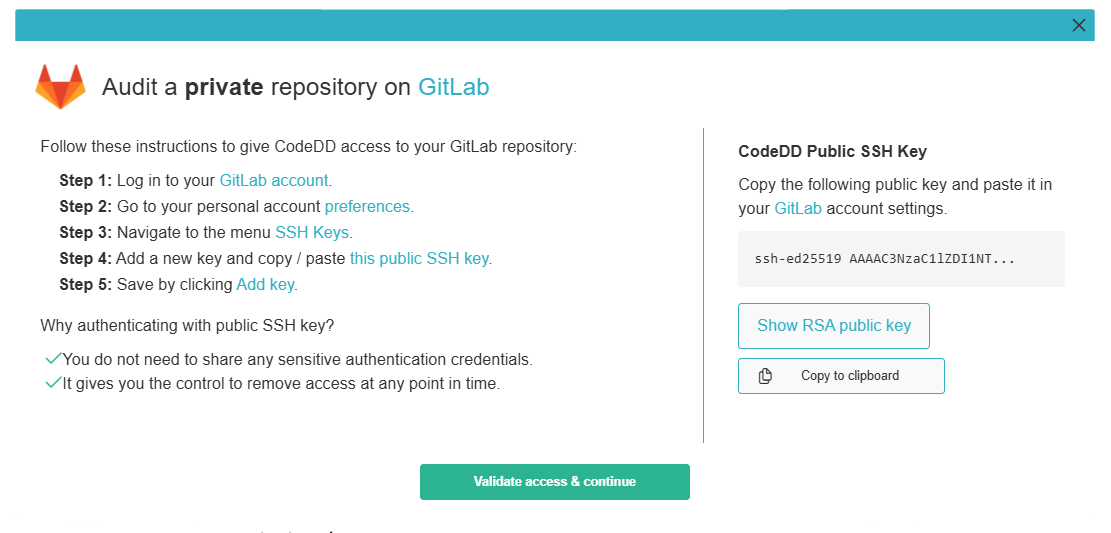
Repository Authentication
Repository Authentication
For private repositories, you will be provided with your unique CodeDD SSH key pair. This key pair will be used to access your repository.
The authentication process is simple and highly secure:
- During registration, a unique SSH key pair is generated for you.
- Add public key to your repository host (GitHub, GitLab, etc.)
- Remove access at any time by deleting the key at your repository host
- CodeDD does not store any credentials, and does not have access to your repository.
Audit Starts - Cloning
Audit Starts - Cloning
CodeDD will clone your repository and start the audit. Your code will be encrypted and stored in a secure and temporary environment.
Security measures in place:
- End-to-end encryption of your source code
- Servers located in Europe (IONOS secure cloud)
- Temporary storage only during audit process
- Automatic deletion after audit completion
Core Analysis
Core Analysis
CodeDD will analyze your code file by file and perform a context analysis. This is done by using state-of-the-art Large Language Models as well as our own fine-tuned models.
Currently, CodeDD uses the following models:
Cleanup
Cleanup
After the audit is complete, the source code is deleted from the temporary environment and the audit report is generated.
No traces of your source code will be left in the system.
Security FAQ for CTOs
Do you clone our repository?
We perform a shallow, ephemeral clone into a chached environment. All source-code files are encrypted using AES-256. Once the analysis is complete (1 - 2 hours), the cache is permanently deleted.
How does the AI interact with our code?
We use enterprise-grade LLM APIs with zero-retention policies. Your code segments are tokenized, analyzed for patterns (scalability, security, debt), and discarded. The AI does not "learn" from your proprietary algorithms.
What access do I need to grant?
We require Read-Only access. You can grant this via a specific Service Account or OAuth token. You remain in control and can revoke access immediately after the scan is initiated.
Is the report confidential?
Yes. The generated "Executive Report" is accessible only to authorized members of the Deal Team designated by the paying client.